GUIDE TO SIGNING IN TO AAMUSTED GMAIL ACCOUNT
Below are the STEPS required to access the AAMUSTED GMAIL system.
- Open any browser.
Type the following, mail.google.com, in the Address bar of the Browser, indicated as 1 in the figure below, and click Enter.
- A front page will appear as below.
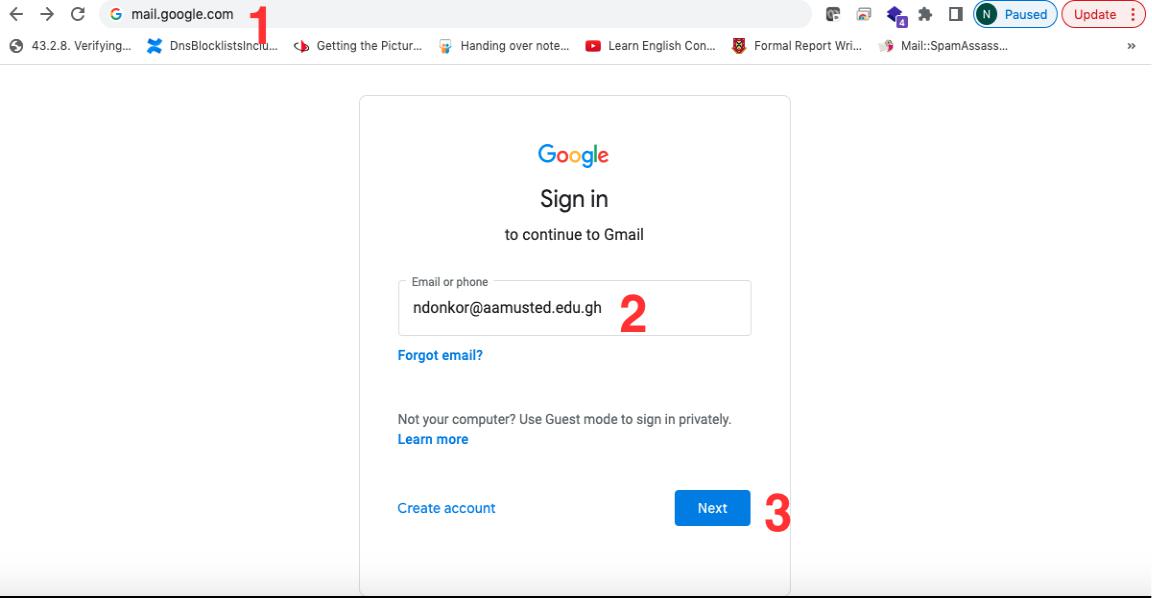
- Enter your aamusted email address, indicated as 2 above (eg. ndonkor@aamusted.edu.gh).
4. Click on the Next button, as indicated in 3 above.
5. A page as below will open for you.
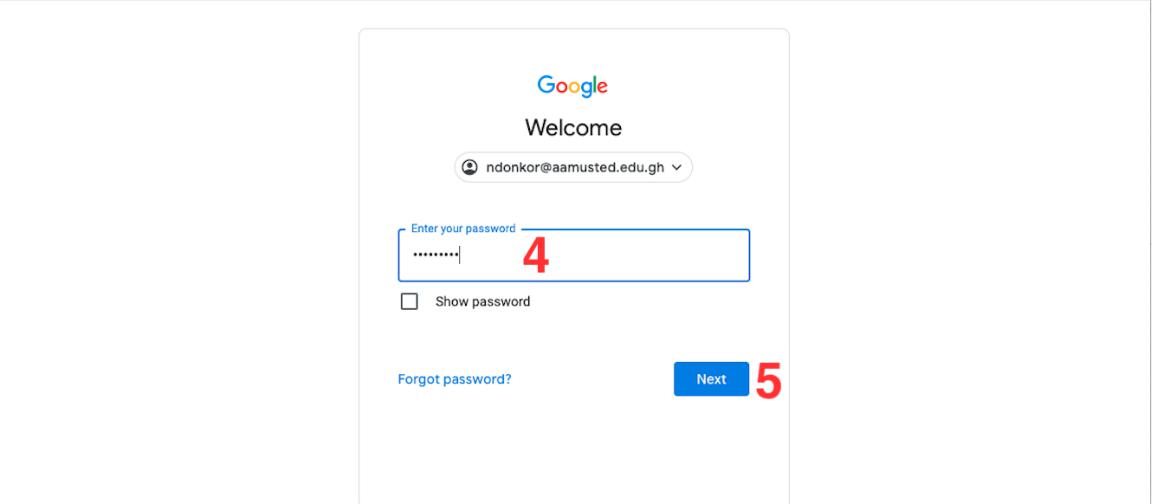
- Enter the default password, which is this, B5h13790t, at the section indicated as 4 in the figure above. (please take note that the password is Case Sensitive).
- Then Click on Next, indicated as 5 in the figure above.
NB: Please those already logged into an existing Google Account in their browser would be sent directly to Step 12 below to continue the processes from there.

- A page will Open as shown in the figure above, and you will be required to enter your personal phone number (please omit the zero, eg. 0264642114 will be 264642114), in the area indicated as 6 in the figure above.
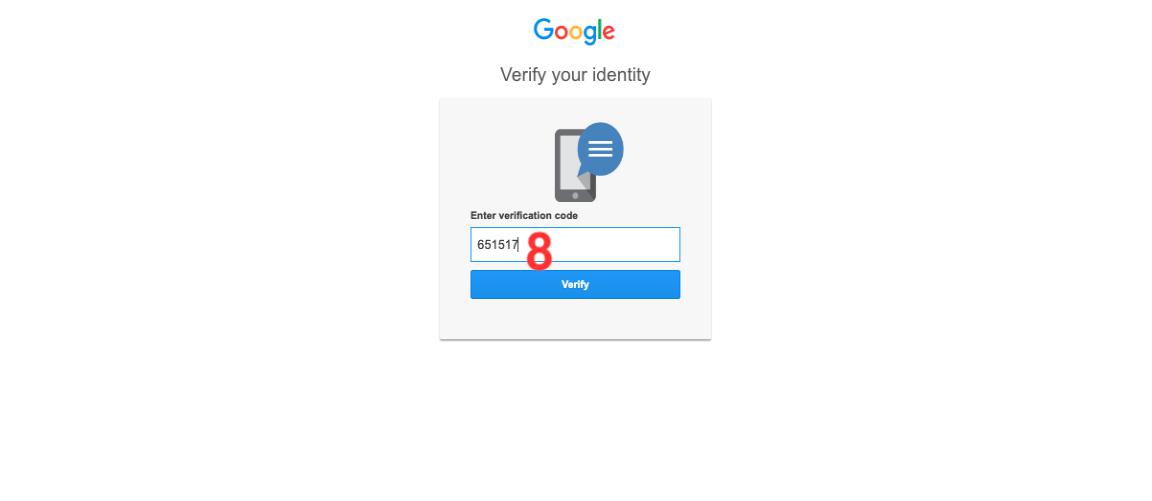
- Click on the Get Code, as shown in 7 above for a code to be sent to your phone.
- A new page will open for you to enter the code sent to your phone. Please kindly enter only the number as indicated in 8 below, then click on the Verify button.
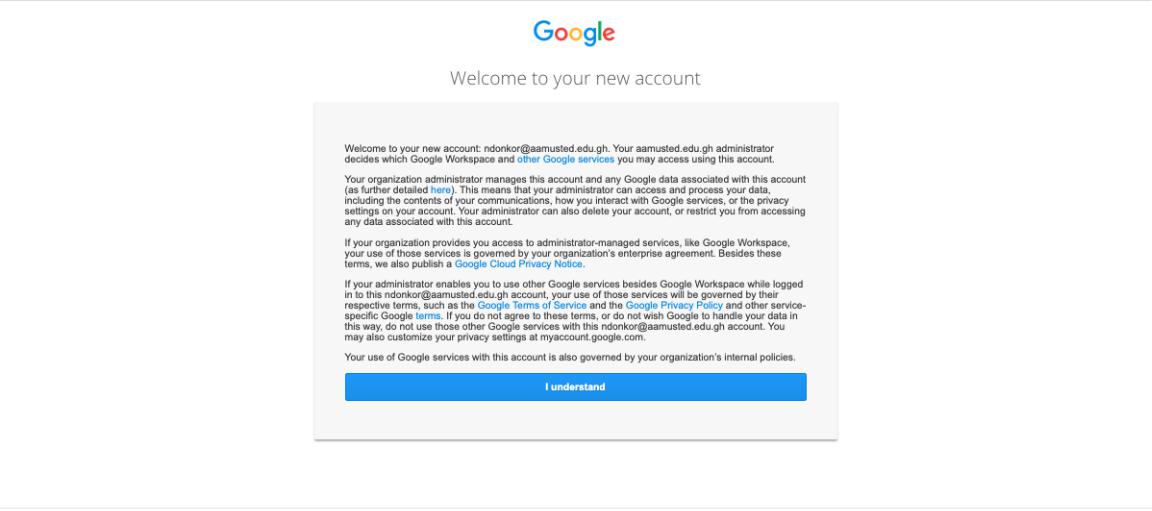
- A new page will open as shown below.
- Click on the I Understand button to then enable your email.
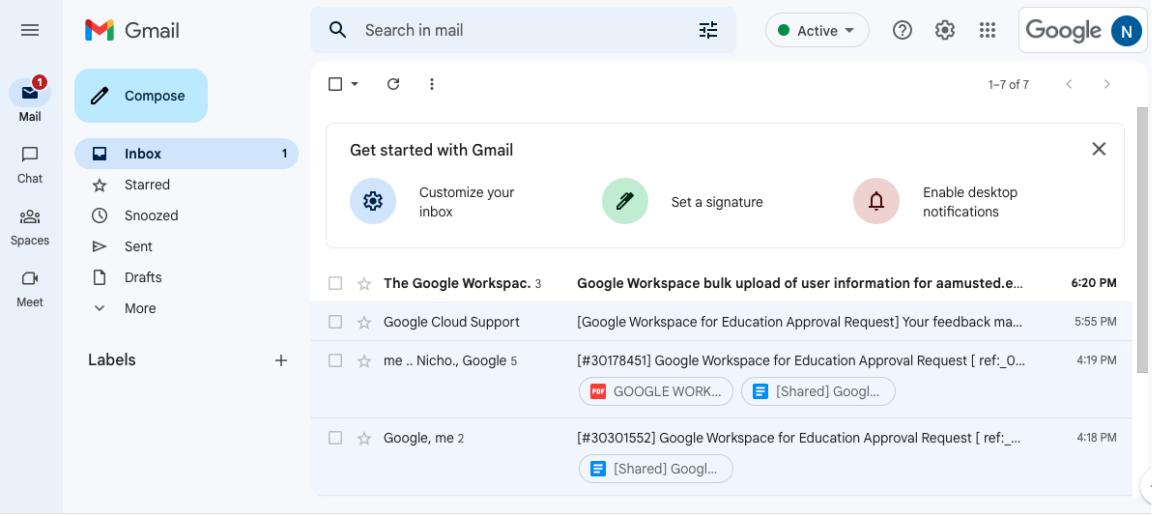
13. Your Email will then Open as shown below.
HOW TO CHANGE YOUR AAMUSTED GMAIL PASSWORD
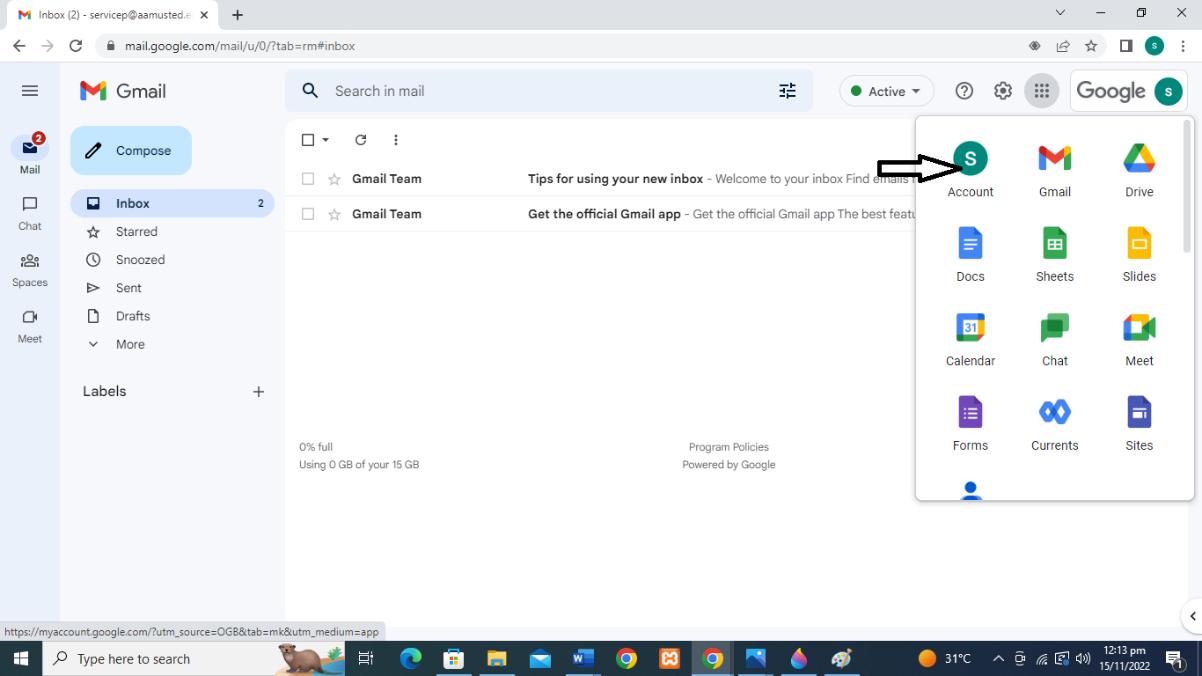
- Open your Google Account. You need to sign in.
- Select “Google apps” as indicated with the arrow below (Google apps icon is shown at the top right of the page as nine dots)

3. Select Account, as indicated with the arrow below
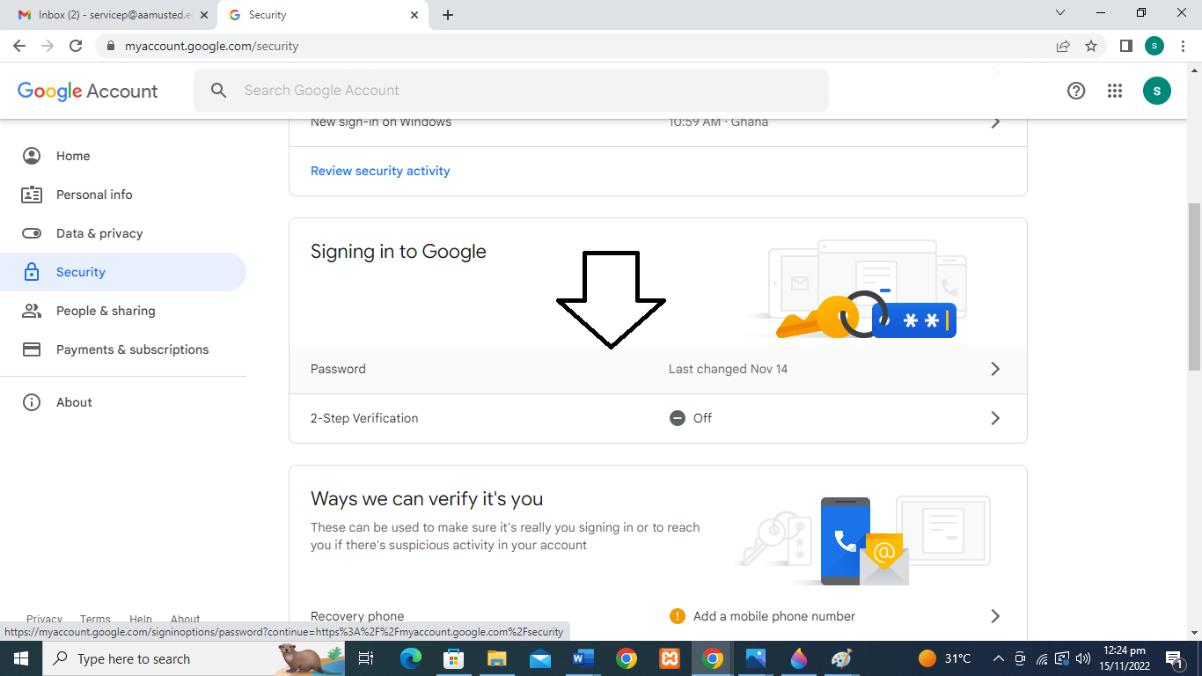
- Click on “Security”.
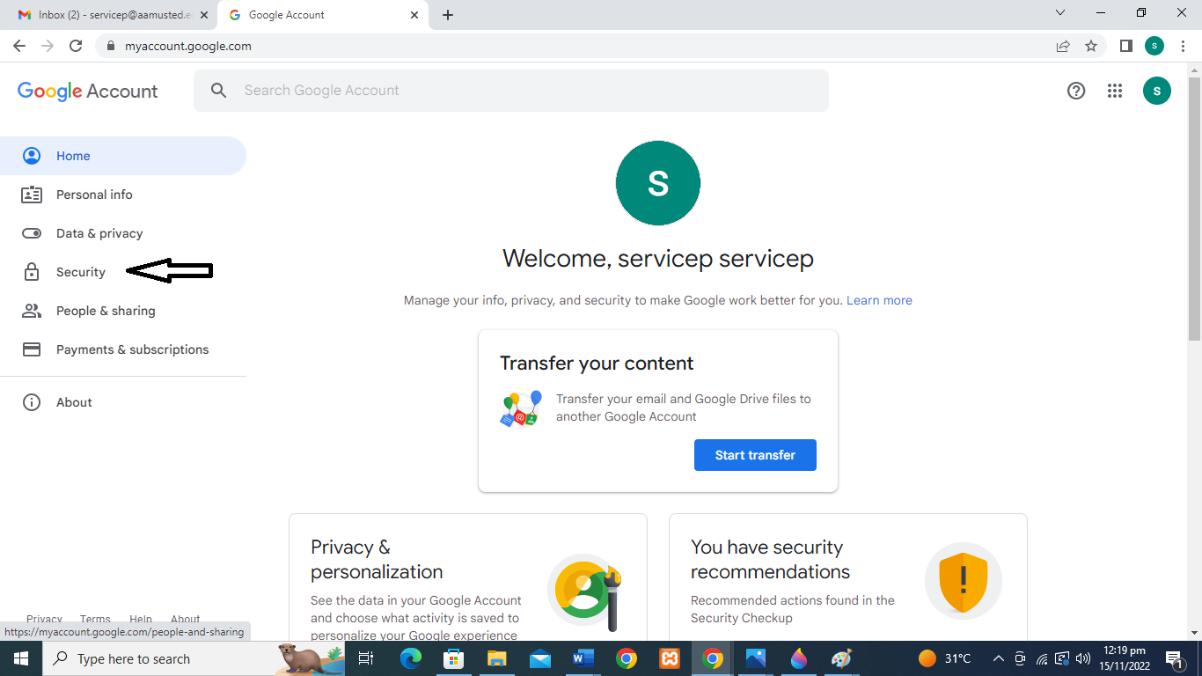
- Under “Security,” go to “Signing in to Google”
- Select Password.
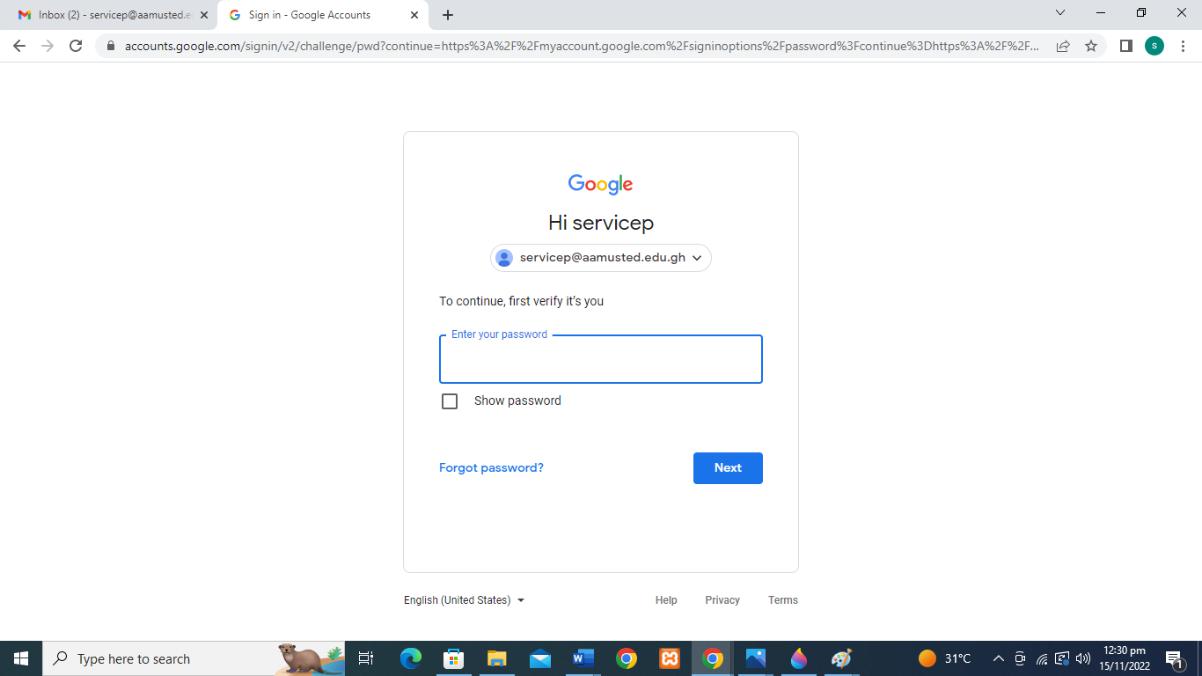
7. Verify your current password on the new page as shown below
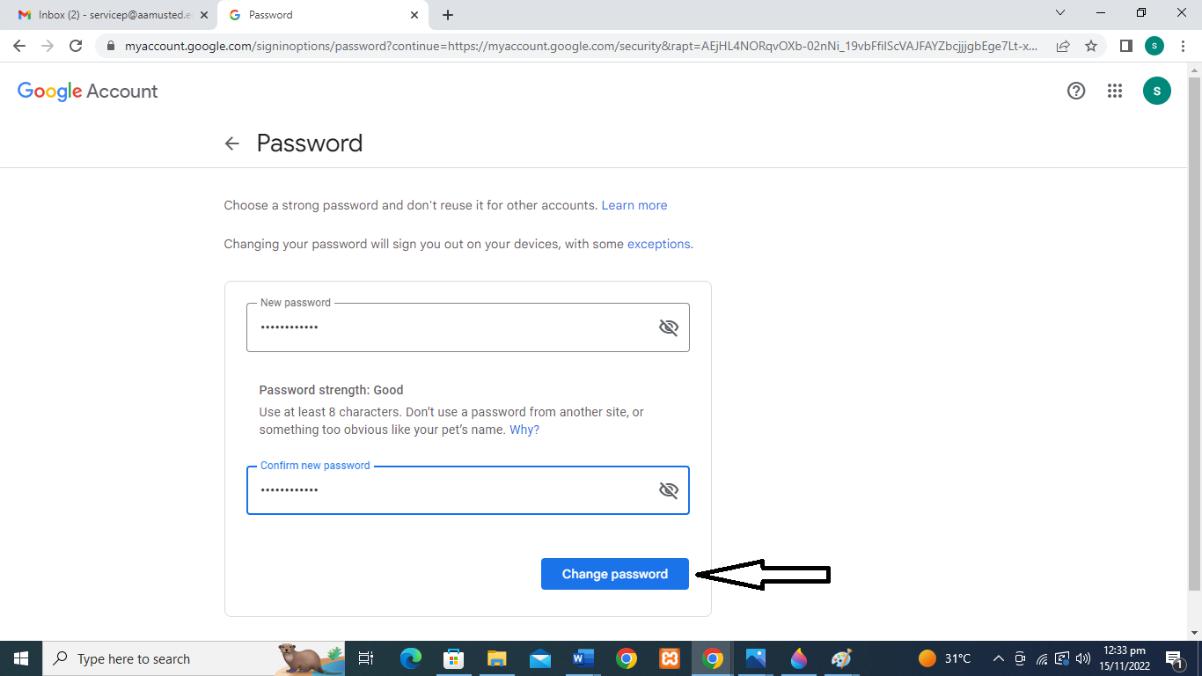
- Enter your new password, Confirm it by reentering in the Confirm new password text area, then select Change Password.
General Guidelines for Creating Passwords
How do you have a “strong” password that is easy to remember? While it may seem tough to do this, there are a few simple tips that can make it easy.
Note: the examples below illustrate just the concepts being discussed. No single technique should be used on its own, but rather should be used with other techniques. The combination of several will produce a strong password.
- Choose something that is easy to remember with a minimum of 8 characters
- Use a mix of alphabetical and numeric characters.
- Use a mixture of upper- and lowercase; passwords are case sensitive.
- Use symbols if the system allows (spaces shouldn’t be used as some applications may trim them away)
- Use a combination of letters and numbers, or a phrase like “many colors” using only the consonants, e.g., mnYc0l0rz or a misspelled phrase, e.g., 2HotPeetzas or ItzAGurl .
- Pick something obscure:
- an odd character in an otherwise familiar term, such as phnybon instead of funnybone;
- a combination of two unrelated words like cementhat
- An acronym for an easy to remember quote or phrase (see below)
- a deliberately misspelled term, e.g., Wdn-G8 (Wooden Gate) or HersL00kn@U (Here’s looking at you).
- Replace a letter with another letter, symbol or combination, but don’t be too obvious about it. Replacing o with 0 or a with 2 or i with 1 is something that hackers just expect. It is definitely better than nothing, but replacing 0 with () would be stronger as it makes your password longer and is not as obvious
- An easily phonetically pronounceable nonsense word, e.g., RooB-Red or good-eits .
- Two words separated by a non-alphabetic, non-numeric, or punctuation character, e.g., PC%Kat or dog,~1#
Choose
You want to choose something that is easy to remember with a minimum of 8 characters that uses as many of the techniques above as possible. One way to do this is to pick a phrase you will remember, pick all the first or last letters from each word and then substitute some letters with numbers and symbols. You can then apply capitals to some letters (perhaps the first and last, or second to last, etc.) You could also perhaps keep or add punctuation.
|
Some examples: |
||
|
Phrase |
First Letters |
Password |
|
So long and thanks for all the fish” |
slatfatf |
5L@tf@tF |
|
“Best Series Ever: Terry Goodkind’s Sword of Truth” |
bsetgsot |
B53:tg’Sot |
|
“You Can’t Have Everything. Where Would You Put It?” |
ychewwypi |
Uch3Wwup1? |
![]()
![]()
![]()
![]()
If you are selecting a password for a website, you may want to incorporate the first few letters of the website name into your password so that every password is different and if one gets out, you don’t have to change them all. This approach has good and bad points.
For example, if you have a standard password like B53:tg’Sot (see above) that you like to use most places (this not recommended), you may modify it by placing the first and last letter of the website around it:
Website Password
![]()
www.ebay.com eB53:tg’Soty
![]()
www.amazon.com aB53:tg’Sotn
![]()
www.webshots.com wB53:tg’Sots
![]()
Do Not Choose…
- Your name in any form — first, middle, last, maiden, spelled backwards, nickname or initials.
- Any ID number or user ID in any form, even spelled backwards.
- Part of your userid or name.
- Any common name, e.g., Sue, Joe.
- Passwords of fewer than six characters.
- The name of a close relative, friend, or pet.
- Your phone or office number, address, birthday, or anniversary.
- Acronyms, geographical or product names, and technical terms.
- Any all-numeral passwords, e.g., your license-plate number, social-security number.
- Names from popular culture, e.g., Harry_Potter, Sleepy.
- A single word either preceded or followed by a digit, a punctuation mark, up arrow, or space.
- Words or phrases with all the vowels or white spaces deleted.
- Words or phrases that do not mix upper and lower case, or do not mix letters or numbers, or do not mix letters and punctuation.
- Any word that exactly matches a word in a dictionary, forward, reversed, or pluralized, with some or all of the letters capitalized, or with any of the following substitutions:
- a -> 2, a -> 4, e -> 3, h -> 4, i -> 1, l -> 1, o -> 0, s -> $, s -> 5, z -> 5
WHY!?
If you only use words from a dictionary or a purely numeric password, a hacker only has to try a limited list of possibilities. A hacking program can try the full set in under one minute. If you use the full set of characters and the techniques above, you force a hacker to continue trying every possible combination to find yours. If we assume that the password is 8 characters long, this table shows how many times a hacker may have to before guessing your password. Most password crackers have rules that can try millions of word variants per second, so the more algorithmically complex your password, the better.
Possible
Character Sets used in Password
![]()
Calculation
![]()
Combinations
![]()
Dictionary words (in english):
(It is debatable but lets generously say
~600,000 words)
![]()
—
![]()
600,000
![]()
Numbers Only
![]()
10^8
![]()
100,000,000
![]()
|
Possible |
||
|
Character Sets used in Password |
Calculation |
Combinations |
|
Lowercase Alpha Set only |
26^8 |
208,827,064,576 |
|
Full Alpha Set |
52^8 |
53,459,728,531,456 |
|
Full Alpha + Number Set |
62^8 |
218,340,105,584,896 |
|
Full Set of allowed printable characters set |
(10+26+26+19)^8 |
645,753,531,245,761 |
![]()
![]()
![]()
![]()
![]()
The longer your password the more secure. If we take the full set of allowed printable characters set (the last line above) and increase the password length, the possible combinations jump exponentially (odd, considering that the calculation includes exponents…)
- 8 Characters > 645,753,531,245,761 (645 Trillion) Combinations
- 9 Characters > 45,848,500,718,449,031 (45 Quadrillion) Combinations
- 10 Characters > 3,255,243,551,009,881,201 (3 Quintillion) Combinations
When we refer to character sets, they are typically numbers, upper and lowercase letters and a given set of symbols. For example:
Characters Number of Characters
![]()
0123456789 10
![]()
abcdefghijklmnopqrstuvwxyz 26
![]()
ABCDEFGHIJKLMNOPQRSTUVWXY 26
![]()
`~!@#$%^&-_=+[{]}. 19
![]()
For Further Assistance, Please contact the following IT staff at the ICT Services Unit.
1.Derrick Kumah ==> 0554433804
2.Obrempong Kodua ==> 0553462381
3.Owusu Olamas ==> 0276822142
To bring IT Services to the doorstep of our cherished users in the University Community, we have setup an IT helpdesk at the IT Services Unit, for proper and effective management of IT related problems and issues at the Campus.
Please do not hesitate to contact us: ictsu@aamusted.edu.gh